- HOME
- PRODUCTS
- SOLUTIONS
- SIRA Certified CCTV
- Mobile Attendance APP
- Payroll Software
- Attendance Management
- Cloud Attendance Solutions
- Access Control Management
- Automatic Parking Barrier
- User Activity Monitoring
- Employee Productivity
- Investigate Employees
- Deter Insider Threats
- Analytics & Monitoring
- Cyber Safety
- Cloud Anti-Virus Software
- COMPANY
- CONTACTS
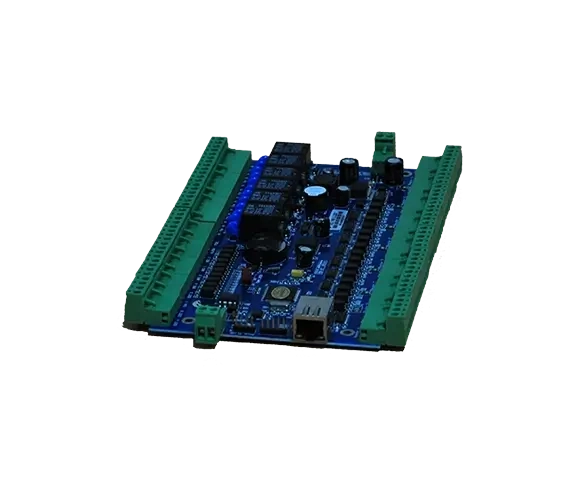
Networked Door Controllers - BMS System
HSIN: HT ACM
With access control BMS system requirements continually evolving, HT ACM remains the most scalable and preferred choice in order to keep-up with rapid changes with compliance, functionality building management system necessities.
- Intelligent Microprocessor based controller
- Easy connectivity with other ELV systems
- Direct Integration with CCTV, Lifts, Fire & Access Systems
- Plenum Rated
- Large capacity - 20K Users & 100K Logs
- Networked for central control
- Free Software Licenses
- Door Access Control Security Powerful & reliable security for access restriction and automation.
- Networked Door Controller Online central management of access control to secured premises.
- Plenum Rated Can be installed in any "air handling" space.
- Scalable and future-proof Designed for Small Office as well Enterprise level usage.
- Perfect adaptability Works with almost all types of slave card readers & Building Management Systems.
- Large Capacity Standard storage of 20,000 users and 100,000 event logs.
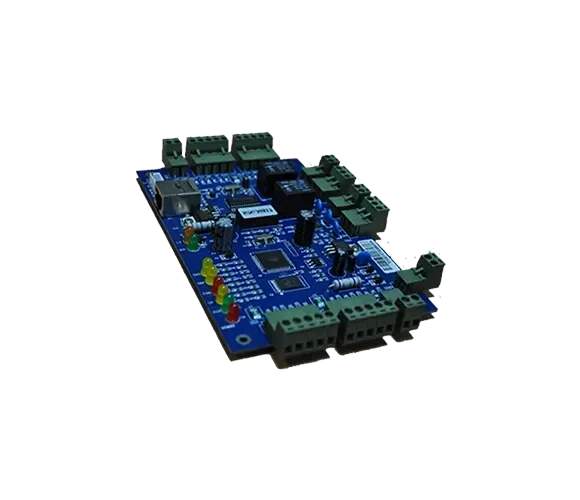
- Extensive variant models 1-door, 2-door, 4 door & 4-door-2-way door controller models.
- Multiple Authentication Modes Supports 9 authenticating & operating modes.
- Built-in web based software On-board software that can be accessed via web interface for all configurations.
- Free Desktop Software Open License Free desktop software for extensive access control reporting.
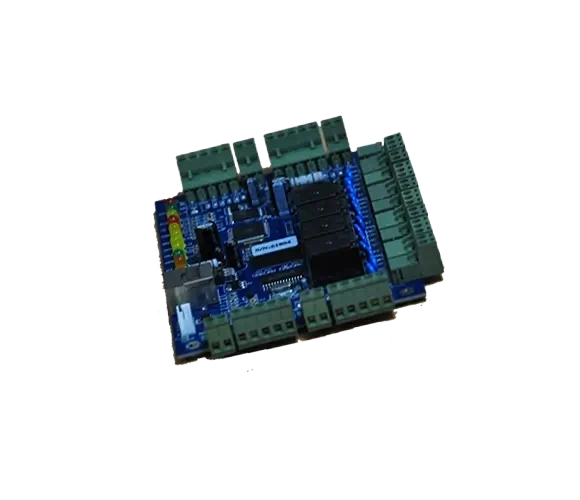
- Robust Security Extensive access control BMS security & alarm settings with various lockdown options. Expansion board to connect with various BMS systems
With access control BMS security requirements continually evolving, HT ACM remains the most scalable and preferred choice to keep-up with rapid changes with compliance, functionality building management system access control BMS necessities.
HT ACM is fully compatible with most of the card readers. It effectively acts as a master door controller and authorizes any type of card, key fob, tag etc, depending on the card reader attached to it. Heyce Access Control Modules (ACM) support multi-function security profiles designed to implement effective access control BMS security.
HT ACM are manufactured in 3 types of control modules viz; 1-door, 2-door & 4 door. Its functions include access control, intrusion monitoring, as well as time clocking. Built-in electronics read Wiegand input data. HT ACM is widely used in access control predominantly due to being quick & economical to install, versatile to network, safe and easy to use.
HT ACM supports 9 authenticating & operating modes: Single card entry, Dual card entry, Single Card + PIN, Dual Card + PIN, ID+PIN. Timed unlock, Keep open, Keep Closed, and Entry/Exit control.
Every HT ACM has onboard software that can be accessed using a web console. Apart from this web based application, HT ACM can also be seamlessly controlled with HT CMPRO® software – a desktop application.
- Anti-pass back & Anti-trail
- Door Interlocking
- Emergency Remote Locking / Unlocking
- 1st Card Access Profiles
- Multi-Card Access Profiles
- Super Password (PIN)
- Flexible pope Dom management
- User Capacity: 20000
- Log Capacity: 100000
- TCP/IP & RS485 Communication Methods
- Built-in power source supplying 12V, 3A to peripherals
- Battery backup support with auto-charge function
- LED notification for all functions.
- Real Time Monitoring & extraction
- Multiple Time-Zone Profile & Access Privileges
- Fire Alarm Integration
- Multi-Alarm Modes (Illegal break-in, Theft Deterrence, long time
- Unlocking, Intimidation, Invalid card Swiping, etc.)
- CCTV Integration Interface
- Access Control BMS integration
- Building Management System integration
- Online Patrol Function
- Custom Map loading
- Flexible, individual & time range pope Dom management
- Real-time photo display, door status display
- Multi-time zone management
- Offline operation
- Real time available staff count
- Quick staff position report
- Alarm support for various flags
- Automatic data upload and collection scheduling
- Time & attendance functions with 99 shifts, multi-overtime & amp; reporting options
- Online patrol & related reports
- Fixed dining functions & related reports
- Interface locking & super password
- Indoor population checkout
Slave Readers

- Mifare Smart Card Reader
- IP68 Rated, Weather Proof
- Strong & Robust Design
Learn More
- Mifare Smart Card Reader
- IP68 Rated, Weather Proof
- Strong & Robust Design
Learn More
- Proximity RFID PIN-Card Reader
- Multiple Form Factors
- Flexible & Compatiable Slave Reader
Learn More
- RFID Card Reader
- Strong Steel & Robust Design
- Responsive LED
Learn More
- Ultra-high Frequency Integrated Radio
- Continuous Tag Reading Distance:≥15mn
- Waterproof Grade:IP65
Learn MoreItem |
Specification |
|---|---|
20,000 users |
Each HT ACM controller can hold up to 20,000 users. A 1-door controller can manage 20,000 users. In a 2-door controller, if door #1 manages 5,000 users, then door #2 can manage a maximum of 15,000 users. Such user distribution applies for a 4-door controller as well. |
100,000 offline event buffers storage |
HT ACM controller has an offline log capacity of 100,000 events. Every event log comprises of information such as card/user ID, time, usage location, authentication action etc. Event logs are stored in FIFO (First In First Out) mode, i.e., once buffer is full, it will start deleting first record onwards. Options to activate/deactivate log recording for push button usage to unlock door and alarm triggering are available. |
Flexible pope Dom management |
System supports access privilege settings that help in defining which user can use which door at what time interval. Specific users who can unlock all doors can be defined. Option to view such pope Dom arrangement report according to door or user is available. This report can be exported to excel format. |
Time range pope Dom management |
Each user can have 3 time segments per day for access control timings. |
Off line operation |
Access control BMS settings can be defined in the software while in offline mode and later uploaded to HT ACM. HT ACM controller stores all uploaded data, comprising of user information, access rights, time profiles, authentication information etc., permanently and operates without computer dependency. |
Real-time monitoring, photo display, door status display |
Real time monitoring feature displays each user & transaction in real time. The displayed data includes:
If external video monitor module is installed, it can record the real time video and photo with every user transaction. |
Real time extraction |
User transaction records can be downloaded into the software in real time. |
Variable door state |
Door state can be defined:
|
Remote door unlocking |
System supports unlocking the door(s) remotely. Log data of such remote unlocking is always stored. |
Interface locking |
Software interface can be locked to prevent un-authorized usage. Alphanumeric password is supported. |
Time link |
If users are required to use more than 3 time segments, system supports unlimited linkage of multi-time segments. For example, if you need different time period on Sat, Sunday to Thursday the time period is 8:30-17:30 but for Sat you need the time period 8:30-12:00, then you can set two different time period, one is Sun to Thurs, 8:30-17:30, another one is Sat 8:30-12:00 and then link this two periods. |
Individual pope Dom revision and upload |
If a new pope Dom is added or existing pope Dom has been revised, the new & amp; revised pope Dom can be uploaded individually. Uploading of other pope Dom is not required. |
Indoor population checkout |
System supports a special feature to check indoor population. The system generates a report showing the number of available people in specified room or multiple rooms. Example 1, if system is used in a mining industry, report showing number people inside the mine can be generated. In the event of emergency, such a report significantly helps the rescue plan. |
Quick position |
Quick position report helps to quickly identify the location of any personnel and how long the personnel stayed at that position. In several companies, personnel are not allowed to use cell phone to check employee location. Quick position report helps in such cases by checking where this person is through his entrance/exit records. |
Card + password |
When used with HT PCR-S-EM salve reader, this system supports dual identification mode of card+ PIN number to enhance security. When Card + PIN mode is implemented, a user can unlock the area with his card along with his unique password. PIN of 1-6 digits is supported. A non-authorized personnel finding any lost card cannot open the door without this unique PIN number, thereby creating a more secure environment. |
Unlock by manually entering the ID / card number + password |
Activation of this function, enables users to enter their card number or ID number with PIN code for identification. |
Super password |
Up to 4 super passwords (PIN) can be issued per door. Personnel can unlock the area with any of these 4 PIN numbers. Caution needs to be taken with these super passwords as the system does not record unlocking information when any super password is used. PIN length can be between 1-6 digits. |
Fire Alarm / Emergency Evacuation |
If HT ACM control panel is connected with I/O expansion board, with receipt of fire switch signal, HT ACM will unlock all the doors it controls and activates the alarm. Such alarm trigger information will be recorded. This enables seamless integration with building management system |
Linkage output |
If control panel connected with I/O expansion board, then when door is unlocked legally, the controller can drive another relay to control more devices connected with access control BMS. For example, with a door unlock, the controller can start up the street light or send a record signal to camera. Linkage relay action time can be set to 0-600 seconds. |
Alarm for illegal break in |
Also called alarm for forced unlocking, this feature enables the monitoring software interface notifies the administrator / control center & computer the alarm time and location and sends sound alerts to the computer. If I/O expansion board is connected to magnetic door sensors, the controller can trigger multiple alarm devices directly. |
Alarm for long time unlocking |
When door is kept unlocked for a long time or any user forgets to close the door, monitoring software interface notifies the administrator the alarm time and location and sends sound alerts to the control center & computer or the access control BMS. The duration required for the door to be unlocked to trigger such an alarm can be defined. The duration for alarm notification to be played can also be defined. |
Intimidation alarm |
When authorized personnel is forced by an intruder to unlock any secured area, he can send a trigger to notify such a forced intrusion by dialing a special PIN known as THREAT CODE. Such a threat code number is different from the user & rsquo;s normal PIN number. When such a threat code is entered, the door unlocks as normal, but in the background an alert is sent to the system administrator / control center & computer or building management system via visual and sound alerts. Such a feature is ideal in high secure environments like banks, cash handling areas etc. |
Alarm for invalid card swiping |
If an invalid or unauthorized card is used, the monitoring software interface notifies the administrator / control center & computer the alarm time and location and sends sound alerts to the computer. |
Anti-pass back and anti-tail |
Anti-pass back feature prevents a card holder from passing his card back to another person to gain entry into the access-controlled area. |
Interlocking |
Interlocking feature is used for access control requirement in which, if a certain door is kept open, the other door cannot be unlocked. A two-door controller can implement interlock feature for two doors; while a four-door controller can implement interlock feature for two doors, three doors and four doors. This feature is ideal for highly secure zones such as banks, cash handling areas etc. |
Multi-card authentication |
Multi-card authentication feature is used for access control bms requirement in which, multiple cards are required to get access into any secure zone. Implementing this feature prevents a single person to open a secured area. Settings can also be made in such a way that you require multiple cards only to enter, but exit can be done by a single card. |
Normal open and normal closing at certain time |
This feature is also called timing mission. Certain public areas such as embassy require the entry/exit point to be normally open during working hours so that the visitors can enter without access restriction and close this entry/exit point beyond public visit timings and let only internal staff to have access. At night, doors need to be closed in such a way that even internal staff is not allowed access. Each controller can apply a maximum of 64 timing missions. This feature can work offline. |
Record unlocking by push button |
System can record the time at which a push button was used to unlock the door. However details of person who used the push button cannot be known. |
Auto download of log data |
Multiple time can be set to automatically download the data from the HT ACM controllers |
Automatically upload pope Dom at scheduled time |
This feature assists in creating time intervals to upload the pope Dom automatically to HT ACM controllers. |
Direct switch between software interface of Office Management and building management |
You can set to switch from the Office Administration interface to access control bms interface. |
Emergency locking |
HT ACM support direct physical connection of emergency locking button. Using such an emergency button helps in lock-down of the entire premises in the cases of emergency. Once emergency locking is activated, even authorized cards will not allow exit from the locked-down area. The system returns back to original state after the emergency button has been disabled. |
Sub-sector administration |
Different department control their own access and time attendance settings and reports. Also the superior administrator can control access and time attendance for all departments. |
Video access control |
If video equipment connected, it can capture the photos and a 3 second video can be recorded when a user uses his card or the push button. This feature helps to check if the right person has used the card to prevent card misuse and buddy punching. |
E-map |
This feature helps in importing the secure area & map and mark each door & location. This allows a more direct and user friendly administration. |
Swiping card to lock and unlock the door |
This features a single card & usage to unlock or power ON and next swipe of same card to lock or power OFF (doors or devices) |
First card unlocking |
This feature helps in deciding which staff is required to be present to unlock the door at the beginning of the day. Example: Some cards can be setup to have the first card unlocking pope Dom, so in the morning only people who have first card unlocking pope Dom can open the door. |
Meeting plan |
System supports in setting the meeting name, address, time, beginning and ending time, meeting contents and meeting notice |
Fill out and revise meeting setting |
System has options to set leave application and manual sign in. Can set meeting members and meeting member's details such as employee, invitation member, auditor etc). Can arrange seat in advance and when the member uses his card, it can display the card holder's name, ID, photo and seat number. |
Real time summary and projection display |
System can generate real time projection, display items such as attendance, absence etc, The summary report can be export into excel format or can be printed out. |
Flexible time setting |
You can set late buffer to allow number of minutes late will not be considered as late. |
Can define holiday period |
You can define the holiday period on the software administration interface |
Define disciplinary measure |
For example: Define how many minutes late or early will be counted as absent |
Can specify a certain door to calculate time and attendance |
Can specify some doors to operate as time attendance and access control and some doors only do access control |
Can set the number of daily card swiping |
You can set each day the user requires to swipe his card at least twice or four times. |
Flexible Sat time and attendance setting |
You can set the weekend to be any day as required. |
Can import leave application form, and customized holiday names |
Can input multiple leave types such as sick leaves, annual leaves etc. |
Manual Log Entry |
Manual logs can be added as whenever required. |
Detai time attendance reports |
System generates multiple time & amp; attendance reports such as raw records, departmental reports, specific period reports etc. System calculates late minutes, number of times late, number of times left early, overtime hours etc. Printing direction can be chosen to print in vertical or horizontal. These reports can be exported to excel format or directly printed. |
Customizing the report forms |
Options of selection to print which item, width, sequence etc available. Custom form settings can be saved for future usage. |
Person excluded from time attendance list |
For example, the general manager or any personnel who is required to go in/out frequently can be excluded from the time attendance calculation in the software. |
Support 99 shifts setting |
Apart from normal shift, the system supports additional 99 different shifts. |
Day Crossing |
System supports day crossing shifts up to 24 hours. |
Every shift can define different card swiping requirements |
Each shift can setup to swipe twice, 4 times, 6 times or 8 times. A certain shift can be defined as overtime work. |
Can calculate two kinds of overtimes: |
Work day overtime means employees who work overtime do not need to swipe at end of their general shift. They only need to swipe their card after they finish their work. Example: normal shift finishes at 17:30 and overtime starts 18:00 onwards. If employee swipes the card at 18:30, then 30 minutes will be counted as overtime. |
- Centralized Biometric Fingerprint Time & Attendance Recording
- Highly Secure Card Access Control Security system
- Automation of complete premise security
- Comprehensive & flexible integration with other security components like CCTV, Intrusion Alarm Systems, building management system etc.
- Improve organizational workflow management
- Realize security compliance requirements
- Protect & efficiently secure highly sensitive areas
- Improve transparency between staff and organization
- Reduce operational costs & improve efficiency
- Prevent misconduct & security negligence
- Seamlessly integrate with emergency and fire detection alarm systems to fully comply with civil defense regulations.